Have been trying to setup an authentication service Mechanism to return a specific Authentication level into WebSEAL, and initially had some trouble, here is what you need to do:
importClass(Packages.com.tivoli.am.fim.trustserver.sts.uuser.Attribute);
importPackage(Packages.com.tivoli.am.fim.trustserver.sts.utilities);
//Optional Trace String - with trace string: com.tivoli.am.fim.trustserver.sts.utilities.*=all
//IDMappingExtUtils.traceString("AuthSvcCred mapping rule called with stsuu: " + stsuu.toString());
var stsuuAttrs = stsuu.getAttributeContainer();
var policyID = context.get(Scope.SESSION, "urn:ibm:security:asf:policy", "policyID");
var isTwoFactorPolicy = false;
if (policyID.equals("urn:ibm:security:authentication:asf:hotp")) {
stsuuAttrs.setAttribute(new Attribute("AUTHENTICATION_LEVEL", null, "5"));
}
The important part are these lines:
if (policyID.equals("urn:ibm:security:authentication:asf:hotp")) {
stsuuAttrs.setAttribute(new Attribute("AUTHENTICATION_LEVEL", null, "5"));
}
Where you specify the policyID, and nominate the appropriate Authentication Level.
My issue occured when I didn’t use “ALL CAPS”, and the Reverse Proxy would generate this:
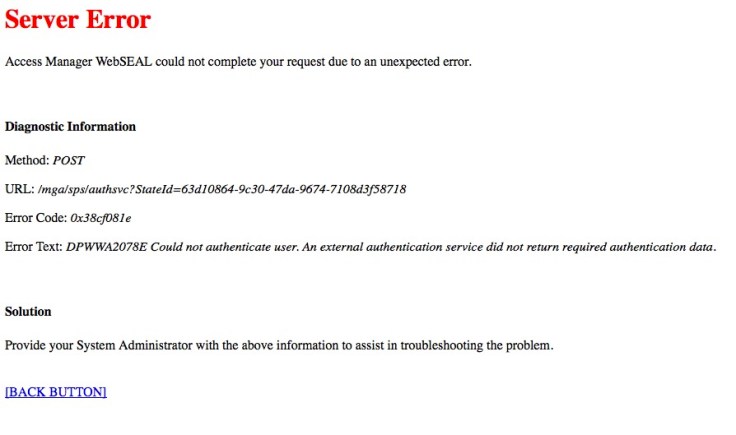
Error Code: 0x38cf081e
Error Text: DPWWA2078E Could not authenticate user. An external authentication service did not return required authentication data.
This appeared because the STSUU already had the AUTHENTICATION_LEVEL attribute, and a second one of different case “authentication_level” was giving it pause.
There is a trace statement in the above mapping rule too, or you can just turn up the trace, and see whats happening:
[User ID [testuser]. Groups [[]]. Attributes [[Name [AZN_CRED_REGISTRY_ID]. Values [[cn=testuser,dc=iswga]]., Name [AZN_CRED_NETWORK_ADDRESS_BIN]. Values [[0xc0a8bc01]]., Name [AZN_CRED_PRINCIPAL_NAME]. Values [[testuser]]., Name [AUTHENTICATION_LEVEL]. Values [[5]]., Name [tagvalue_max_concurrent_web_sessions]. Values [[unset]]., Name [tagvalue_login_user_name]. Values [[testuser]]., Name [tagvalue_user_session_id]. Values [[aXNhbTkwLXdlYnNlYWwA_VrBmJwAAAAIAAAAwl38AAGghArSXfwAAZ2tQaTllSVM3OEJ0TUgzS2pJNTY5MkViSlpQd2lGQXl6VkduU3FaTlB6aGIya2Rq:default]]., Name [AZN_CRED_AUTH_METHOD]. Values [[password]]., Name [AZN_CRED_NETWORK_ADDRESS_STR]. Values [[192.168.188.1]]., Name [AZN_CRED_AUTHNMECH_INFO]. Values [[LDAP Registry]]., Name [AZN_CRED_MECH_ID]. Values [[IV_LDAP_V3.0]]., Name [authenticationTypes]. Values [[urn:ibm:security:authentication:asf:hotp]]., Name [tagvalue_session_index]. Values [[6efd70b0-c985-11e5-9105-000c297edf67]]., Name [authenticationMechanismTypes]. Values [[urn:ibm:security:authentication:asf:mechanism:hotp]]., Name [AZN_CRED_IP_FAMILY]. Values [[AF_INET]]., Name [AZN_CRED_QOP_INFO]. Values [[SSK: TLSV12: 2F]]., Name [AZN_CRED_PRINCIPAL_UUID]. Values [[bb809254-8e8a-11e5-aeb2-000c297edf67]]., Name [AZN_CRED_VERSION]. Values [[0x00000900]]., Name [AZN_CRED_BROWSER_INFO]. Values [[Mozilla/5.0 (Macintosh; Intel Mac OS X 10.11; rv:44.0) Gecko/20100101 Firefox/44.0]]., Name [AZN_CRED_AUTHZN_ID]. Values [[cn=testuser,dc=iswga]]., Name [AZN_CRED_PRINCIPAL_DOMAIN]. Values [[Default]].]].].
