My friend Leo has just posted details on how to make use of the OAuth provisioning APIs exposed via Infomap, you can take a look at the details here: https://www.ibm.com/blogs/security-identity-access/2018/06/oauth-building-developer-portal/ This is one of the best things you can do to enable your ISAM infrastructure to be easily consumed by your organizations developers. They can... Continue Reading →
ISAM OAuth Inactivity
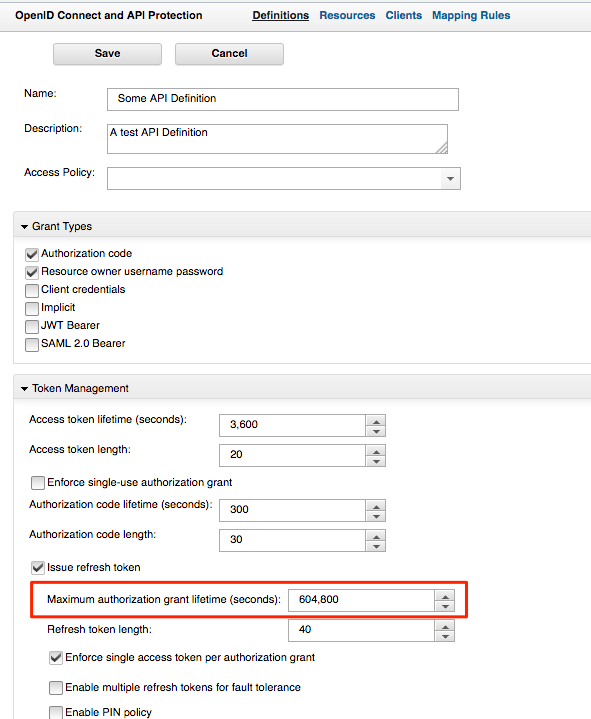
Its not immediately obvious, and commonly misconstrued as an problem of disappearing tokens, but the OAuth grants in ISAM have a "Maximum" Grant lifetime, as opposed to an inactivity in a default API Definition. This means that when you request a Token - say via ROPC and you are using the default settings of an... Continue Reading →
ISAM – Infomap – Any alias authentication
A number of customers like to use various alias's to authenticate into ISAM, up until recently, the primary way of achieving this, is via a Custom EAI, or some elaborate LDAP hackery. Infomap, and the UserHelper capabilities, makes this a much easier affair. Here is an example, where we use the infomap to authenticate based... Continue Reading →
ISAM Mapping Rules – Accessing Server Connection Details
With the release of ISAM 9.0.2.1, it's now possible to access connection details from an appliances Server connection in a JavaScript mapping rule: This means you can now write more portable mapping rules, where the configuration details for an environment can be stored in appliance level configuration, rather than your mapping rules. Accessing the values... Continue Reading →
ISAM Basic Users (aka Lite Users) vs Federated ISAM users
ISAM introduced the concept of non-imported users which we named Basic users, or lite users depending on who you ask, back in 2014 with version 8.0.0.4. I still regularly receive a bunch of questions as to what this means from an architectural perspective, and most importantly, what are the advantages and disadvantages to this new... Continue Reading →
Commonly Overlooked ISAM Settings for production deployments
The ISAM Reverse Proxy has a wealth of settings that can be configured. This means that almost every deployment situation can be catered for, but also means that its easy to overlook some settings that may give you grief. In this post, I've decided to capture some of the more important ones to help you... Continue Reading →
ISAM HTTP XSL Transformation Rule to Modify request Parameters
I had to write an XSL Stylesheet to modify a request parameter - I had to modify a request parameter in a TFIM SAML request from RelayState to Target, here is what I used changing request text from "something" to "another": <?xml version="1.0" encoding="UTF-8"?> <xsl:stylesheet xmlns:xsl="http://www.w3.org/1999/XSL/Transform" version="1.0"> <!-- This is a template stylesheet which should... Continue Reading →
Advanced ISAM Session Timeout capabilities
Sometimes it might be necessary to manage a session lifetime based on business or security factors, and these might need to be specific to an operation in progress. Here are some helpful techniques for managing the timeouts more dynamically: Understanding Session timeout accuracy Before we go into more detail of setting the session timeouts - it's... Continue Reading →
ISAM LMI REST API – HTTP 405 Method not Allowed Error
When using the REST API to run some commands against an ISAM for Web/Mobile Appliance, I ran into an HTTP error code that wasn't immediately obvious. Status Code: 405 Method Not Allowed There was no issue with the POST Method, but rather the headers that I sent. It's vitally important that you send the "Accept"... Continue Reading →
IBM Security Access Manager (ISAM) Kerberos Configuration Guide
My colleague has posted an in depth set of articles on IBM DeveloperWorks for Kerberos configuration with ISAM. It covers both Kerberos integration's, being Desktop SSO with Kerberos into ISAM, and junctioning to servers using Kerberos for Junction SSO. The article is available here: https://www.ibm.com/developerworks/community/wikis/home?lang=en#!/wiki/W746177d414b9_4c5f_9095_5b8657ff8e9d/page/Information%20and%20Guides%20for%20Kerberos%20SSO
ISAM Forms SSO into BMC Remedy
Updated 09/2015: HTTP 505 error solved. See end of article. On a customer site, I encountered BMC Remedy, and had to perform SSO into the Application from ISAM. My initial attempt included trying to use the standard integration we have with Tomcat versions, as detailed here: http://www-01.ibm.com/support/docview.wss?uid=swg24021393 Unfortunately, this didn't work in the time I'd... Continue Reading →
OAuth Authorization
When using ISAM in OAuth patterns, there are a number of ways you can do authorization based on OAuth scopes. In general, at last check, there are three main ways of Authorizing OAuth requests based on their scope. (or other attributes associated with the tokens). The mechanisms available are dependent on which OAuth validation mechanism... Continue Reading →
ISAM for Web without a User Registry – New and Improved
In 2009, Shane Weeden posted an article about using WebSEAL without a user registry. The article made use of a number of components, including TFIM as a mechanism to generate an ISAM credential and return that to WebSEAL to build a session. This pattern is particularly useful in scenarios where the users are stored in... Continue Reading →
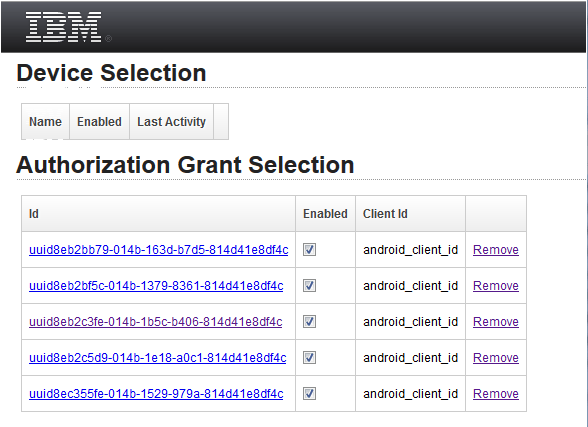
Cannot delete OAUTH grants and devices on ISAM for Mobile
When using ISAM for Mobile, and you access the User Self Service/User Self Care pages for managing OAuth Grants, there is the option to delete and manage your grants. https://<ISAM for Mobile Host>/mga/sps/mga/user/mgmt/html/device/device_selection.html In earlier versions of ISAM for Mobile, the configuration prevented DELETE and PUT operations. This meant that WebSEAL would not allow the... Continue Reading →
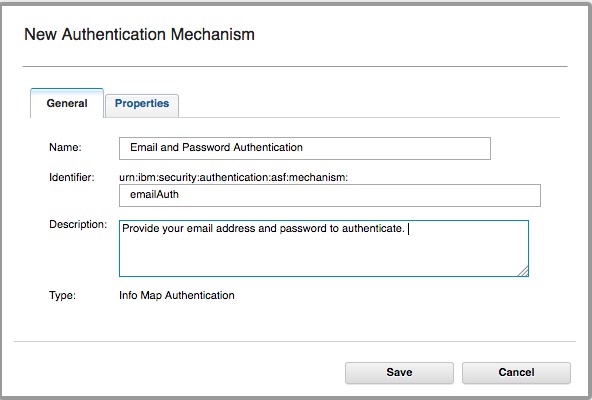
ISAM for Mobile – ROPC OAuth Username and Password Validation
As of V8.0.1.0 of ISAM for Mobile, there is a helper class in the Javascript mapping rule for Resource Owner Password Validation against the configured LDAP server. There are a few steps required to configure it though. If you haven't configured it, you will receive the following error on attempting an ROPC flow: {"error":"mapping_error", "error_description":"com.tivoli.am.rba.exception.RBARuntimeException:... Continue Reading →