How do you handle a partially authenticated state when the inbound user is either missing attributes, or needs to select from multiple mapped accounts when accessing resources protected by ISAM or what is now IBM Security Verify Access.
Using ISAM with a Single Page Application (SPA)
Over on the ISAM blog on ibm.com, I've just completed an indepth article on using ISAM with a Single Paged Application. These are typically applications that use JavaScript, AJAX, Angular and other frameworks to make a very dynamic user experience on a website. Think of any site you've used where the whole page doesn't reload... Continue Reading →
ISAM – Redirect on Logout or show login page on logout
A simple post here - a quick guide on how you redirect to a specific url after logging out. In the ISAM reverse proxy, you can make use of the operation based Local Response Redirect, to send you to a specific location once you have logged out. To enable this, enable local response redirect, #--------------------------... Continue Reading →
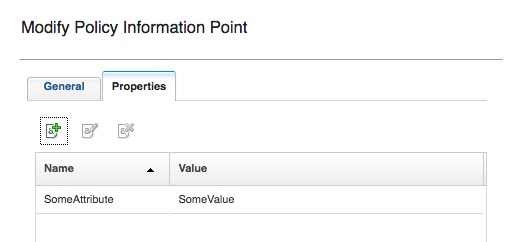
ISAM AAC CBA PIPs – Accessing config options
Ive had people occasionally ask, - how do I access the configuration panel attributes in our JavaScript PIP. Accessing them is fairly straightforward, just use the 'config' object.
ISAM – Infomap – Any alias authentication
A number of customers like to use various alias's to authenticate into ISAM, up until recently, the primary way of achieving this, is via a Custom EAI, or some elaborate LDAP hackery. Infomap, and the UserHelper capabilities, makes this a much easier affair. Here is an example, where we use the infomap to authenticate based... Continue Reading →
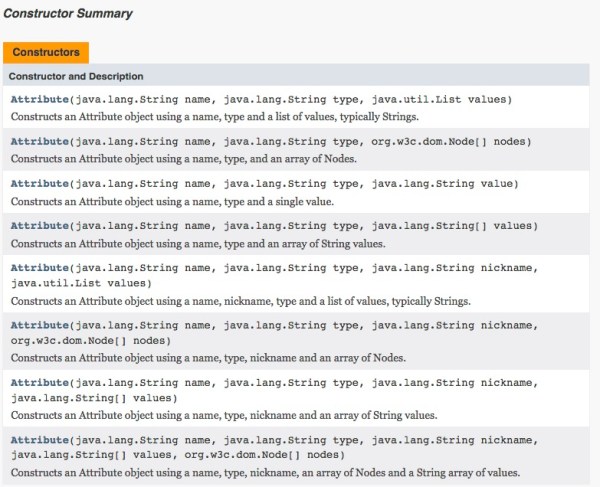
ISAM JavaScript – Making Multi value Attributes
Received a question related to the 'art' of making an attribute that is multivalued for the purpose of a SAML Mapping rule, but this is still relevant when using Infomap, OAuth or even the AuthSvcCred mapping rules. When we are writing the JavaScript mapping rules, the engine wants to make JavaScript objects, this is useful... Continue Reading →
OAuth Auth – Credential Enrichment and HTTP Header Sending
If you wanted to add HTTP Headers to the junctioned request, similar to how the old OAuth EAS used to. For example sending the Client ID, or the Token details as HTTP headers, there is an easy way to do this from the OAuth Mapping rule. Here I am not only adding things like the... Continue Reading →
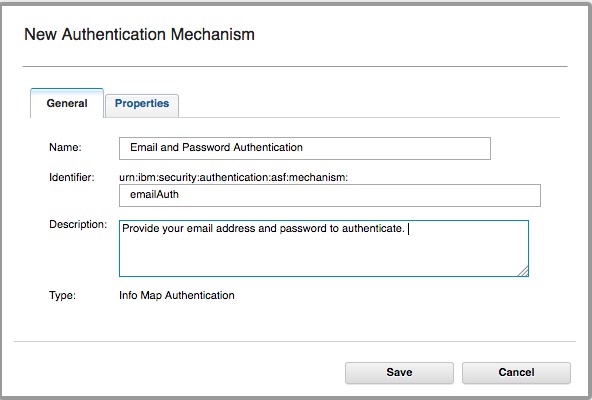
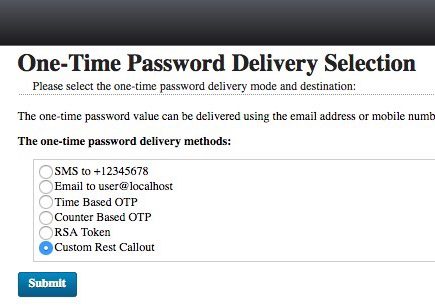
ISAM create a new OTP Mechanism
I wanted to make a new OTP Mechanism that was called by a JavaScript REST call - that wasn't the SMS mechanism in the box. In this example - I tested it with Boxcar - an iOS App that lets you send Push notifications with a simple REST call. To add a custom mechanism to... Continue Reading →
ISAM Mapping Rules – Accessing Server Connection Details
With the release of ISAM 9.0.2.1, it's now possible to access connection details from an appliances Server connection in a JavaScript mapping rule: This means you can now write more portable mapping rules, where the configuration details for an environment can be stored in appliance level configuration, rather than your mapping rules. Accessing the values... Continue Reading →
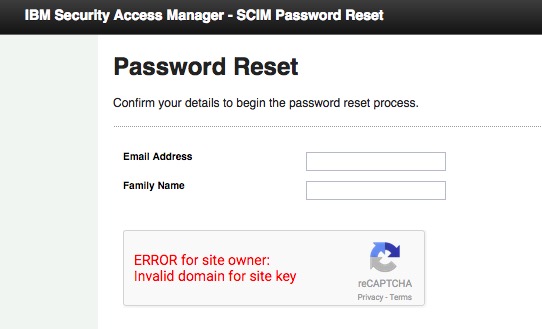
Password Reset with ISAM User Self Care
In ISAM 9.0.2, we released native appliance based capabilities to perform User Self Care Operations with ISAM. The user self care operations are built using the authentication service which means operations are modular, can easily be reordered or customised to suite your flow. Out of the box, there are three USC operations included: USC Account... Continue Reading →
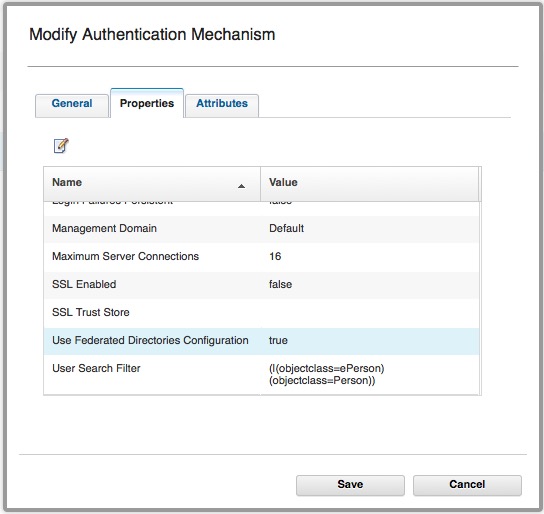
Using Basic Users with OAuth-Auth and ROPC
It is possible to use Basic Users with the ISAM OAuth-Auth capabilities. (ISAM Basic users are users that have NOT been imported into the ISAM registry.) Authentication used to be performed by: isAuthenticated = PluginUtils.isValidUsernamePassword(username, password); I've talked about how this is configured here. This authentication mechanism *can* be configured to use Federated Registries, however... Continue Reading →