It is possible to use Basic Users with the ISAM OAuth-Auth capabilities. (ISAM Basic users are users that have NOT been imported into the ISAM registry.)
Authentication used to be performed by:
isAuthenticated = PluginUtils.isValidUsernamePassword(username, password);
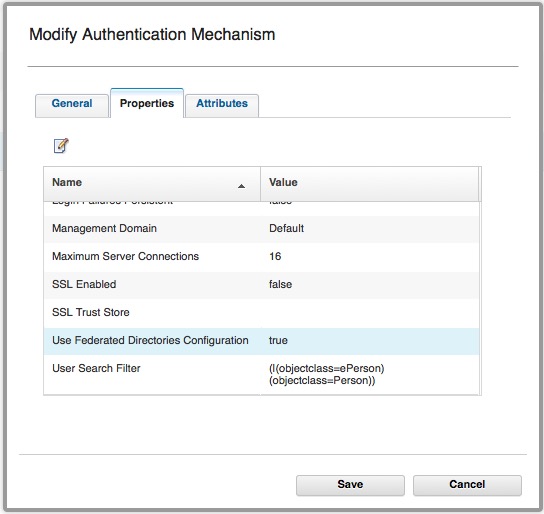
I’ve talked about how this is configured here. This authentication mechanism *can* be configured to use Federated Registries, however it requires the users to have been imported into ISAM via pdadmin.
However since ISAM 9.0.4.0 we now use the UserLookupHelper for authentication in OAuth, (Assuming you’re using the new ISAM 9.0.4+ default mapping rules) (UserLookupHelper has been around since 9.0.2.1, so can still work at that version, just need to use the authenticate commands from there).
Details from the Knowledge Center feature:
Use Federated Directories Configuration
Set this option to true to use the configured federated directories when authenticating a user name and password. If you specify true:
- The LDAP Host Name and LDAP Port properties must define a Security Access Manager user registry. This is typically the user registry of the runtime component.
- The users in any of the additional federated directories you configure must exist in the user registry of the runtime component. Therefore, import these users, if necessary.
Data type: Boolean
Default: false.
Alternative Workaround:
As an alternative for user authentication, we can use an ISAM reverse Proxy to authenticate a user via the Mapping Rules HTTP Callout capability. A demo of this feature is included in the default Pretoken mapping rule for the configured API Protection Policy. If you conifgure the Mapping rule to validate against an ISAM reverse proxy instance that has been configured with Basic User support, then we can satisfy the authentication process.
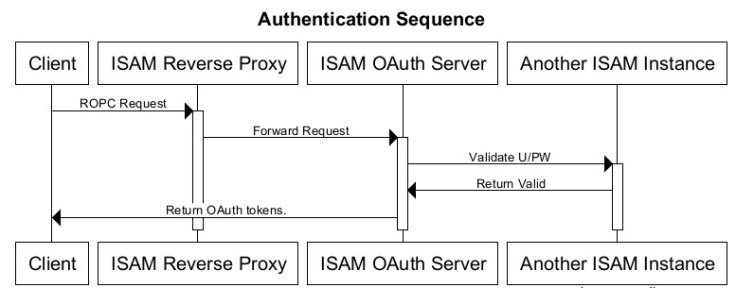
The mapping rule can do one of two things:
A) Validate using Basic Auth against the other ISAM instance.
B) POST to the /pkmslogin.form on the other instance.
I plan to update this article with a mapping rule doing the above soon.
