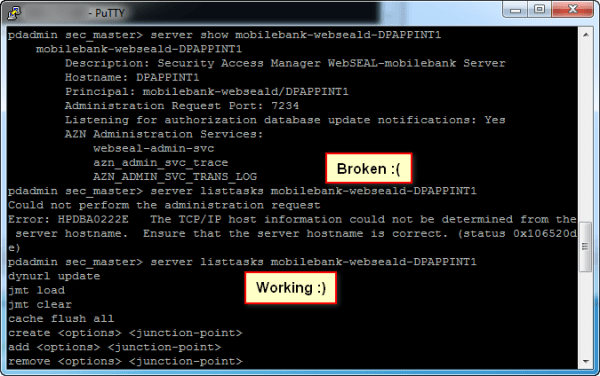
I started experimenting with ISAM for DataPower today, and in doing so, encountered a fun bug based on my environment. When creating a Junction, nothing appeared to happen. Eventually in attempting to debug using pdadmin on the DP Commandline interface, I ran the command: pdadmin sec_master> server listtasks mobilebank-webseald-DPAPPINT1 Could not perform the administration request... Continue Reading →
ISAM Appliance Networking Changes
In ISAM v8.0.1.2, some fairly significant changes were introduced to the Management of the ISAM appliance networking interfaces. The update removed the concept of separate NICs for Application and Management interfaces and instead bound those concepts to an IP Address. It added support for VLAN tagging on packets, and provides a number of enhancements around... Continue Reading →
Determine ISAM Appliance MAC Address
It can be a little confusing to get the MAC Address of the ISAM appliance network interfaces, which is particularly useful in virtualised environments. I've been in circumstances where you want to add/remove networking interfaces, but the order in which they are described in VMWare rarely corresponds to the order they are assigned when the... Continue Reading →
OAuth Authorization
When using ISAM in OAuth patterns, there are a number of ways you can do authorization based on OAuth scopes. In general, at last check, there are three main ways of Authorizing OAuth requests based on their scope. (or other attributes associated with the tokens). The mechanisms available are dependent on which OAuth validation mechanism... Continue Reading →
ISAM Authorization Rule for OAuth Scope
The vast majority of the work in developing this Authorization Rule was developed by my colleague Shane Weeden. Thanks for sharing Shane! Find more of his work here: https://www-304.ibm.com/connections/blogs/sweeden/?lang=en_us This authorization rule extracts the OAuth values of scope from the ISAM credential and applies a TRUE or FALSE authorization result subject to it containing the... Continue Reading →
ISAM Context Based Access PIP for OAuth
The vast majority of the work in developing this PIP was done by my colleague Scott Andrews. Thanks for sharing Scott! Find more of his work here: https://ibm.biz/securityintegration Building from the example PIP in my article here: ISAM JavaScript Policy Information Points here is a PIP that extracts the OAuth values of scope and supplies... Continue Reading →