Branded SMS and Email OTP messages with IBM Security Verify Access just takes a few steps with IBM Security Verify Access. First thing you need to do - is determine how you plan to differentiate the inbound request from a different brand. In this example, we'll do it based on an inbound HTTP header to... Continue Reading →
ISAM – Infomap – Any alias authentication
A number of customers like to use various alias's to authenticate into ISAM, up until recently, the primary way of achieving this, is via a Custom EAI, or some elaborate LDAP hackery. Infomap, and the UserHelper capabilities, makes this a much easier affair. Here is an example, where we use the infomap to authenticate based... Continue Reading →
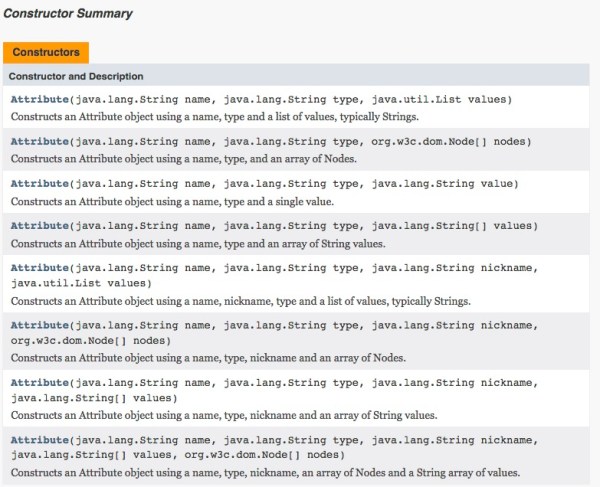
ISAM JavaScript – Making Multi value Attributes
Received a question related to the 'art' of making an attribute that is multivalued for the purpose of a SAML Mapping rule, but this is still relevant when using Infomap, OAuth or even the AuthSvcCred mapping rules. When we are writing the JavaScript mapping rules, the engine wants to make JavaScript objects, this is useful... Continue Reading →
OAuth Auth – Credential Enrichment and HTTP Header Sending
If you wanted to add HTTP Headers to the junctioned request, similar to how the old OAuth EAS used to. For example sending the Client ID, or the Token details as HTTP headers, there is an easy way to do this from the OAuth Mapping rule. Here I am not only adding things like the... Continue Reading →
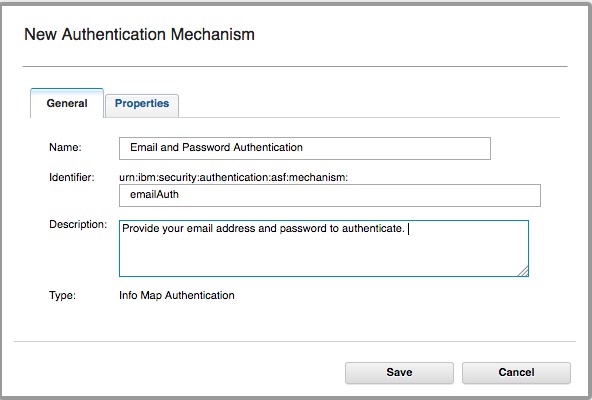
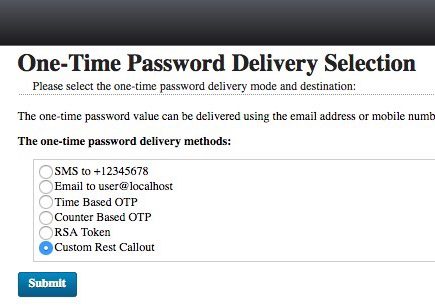
ISAM create a new OTP Mechanism
I wanted to make a new OTP Mechanism that was called by a JavaScript REST call - that wasn't the SMS mechanism in the box. In this example - I tested it with Boxcar - an iOS App that lets you send Push notifications with a simple REST call. To add a custom mechanism to... Continue Reading →
ISAM Mapping Rules – Accessing Server Connection Details
With the release of ISAM 9.0.2.1, it's now possible to access connection details from an appliances Server connection in a JavaScript mapping rule: This means you can now write more portable mapping rules, where the configuration details for an environment can be stored in appliance level configuration, rather than your mapping rules. Accessing the values... Continue Reading →
Get Headers and Cookies in JavaScript InfoMap Mechanism
In a previous post, I shared a way to get headers in OTP mapping rules and in the AuthSvcCred Mapping rules. Since the infomap module is a little bit different, I have included an example of how you can do it there: Here is the output into my MACRO for easy debugging: User-Agent: Mozilla/5.0 (Macintosh;... Continue Reading →
ISAM OAuth – Get credential attributes during an Authorization Code Flow
When performing an Authorization Code flow, or when performing an Implicit Grant flow, it may be necessary to get attributes out of the ISAM Session credential, and store them with your OAuth tokens. This is a quick guide to show how this can be done: Identify the request in the mapping rule Requests passing through... Continue Reading →
ISAM OAuth Token Mapping Rules – Beginners Guide
The ISAM OAuth implementation is exceedingly flexible. If you are just looking to do basic OAuth flows, then chances are you won't ever even look in these OAuth Mapping Rules. On the other hand, if you're looking to modify the behaviour of the OAuth flow to achieve OAuth nirvana, then these Mapping Rules are going... Continue Reading →
ISAM AAC OAuth Session Endpoint
ISAM Advanced Access Control has a mechanism that allows a developer to convert an authenticated/valid OAuth Access token, into an authenticated ISAM session, that is using a cookie. There are two useful scenarios that this endpoint comes in handy: Hybrid Apps Where an OAuth authenticated native application wants to open a WebView, that is authenticated... Continue Reading →
Commonly Overlooked ISAM Settings for production deployments
The ISAM Reverse Proxy has a wealth of settings that can be configured. This means that almost every deployment situation can be catered for, but also means that its easy to overlook some settings that may give you grief. In this post, I've decided to capture some of the more important ones to help you... Continue Reading →
ISAM Federations – Using an Email address as the SAML Principal Name
Encountered a scenario last week, where I logged the user into ISAM using an AD Short name, but needed to use the email address as the SAML Principal name when logging into an external service (e.g. Pager Duty). The user's email address was populated as an attribute in Active Directory, and ISAM will automatically pull... Continue Reading →
Set an authentication level for an Authentication Service Mechanism
Have been trying to setup an authentication service Mechanism to return a specific Authentication level into WebSEAL, and initially had some trouble, here is what you need to do: The important part are these lines: if (policyID.equals("urn:ibm:security:authentication:asf:hotp")) { stsuuAttrs.setAttribute(new Attribute("AUTHENTICATION_LEVEL", null, "5")); } Where you specify the policyID, and nominate the appropriate Authentication Level.... Continue Reading →
OAuth Auth ISAM authentication level mapping
ISAM provides the concept of Authentication Levels out of the box. This means a given authentication mechanism or flow can be assigned an integer value >0 that represents the authentication strength. OAuth Auth can make use of this for features such as incremental authentication - for example if the OAuth grant was issued via single... Continue Reading →
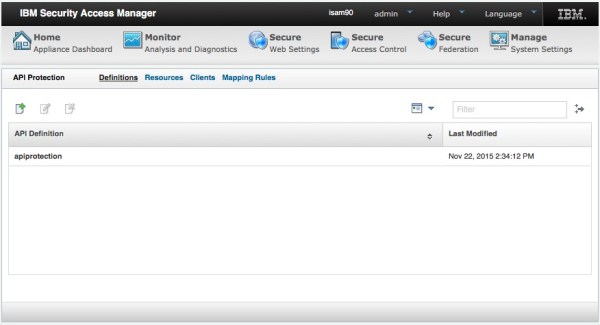
OAuth Authorization
When using ISAM in OAuth patterns, there are a number of ways you can do authorization based on OAuth scopes. In general, at last check, there are three main ways of Authorizing OAuth requests based on their scope. (or other attributes associated with the tokens). The mechanisms available are dependent on which OAuth validation mechanism... Continue Reading →