HTTP Public Key Pinning is a header that allows you to pin a certificate to a host, consider it the next step after HSTS ISAM for Web & Sending Security HTTP Headers the solution isn't any different to send the header with WebSEAL. The HTTP Public-Key-Pins response header associates a specific cryptographic public key with... Continue Reading →
OAuth Auth – Credential Enrichment and HTTP Header Sending
If you wanted to add HTTP Headers to the junctioned request, similar to how the old OAuth EAS used to. For example sending the Client ID, or the Token details as HTTP headers, there is an easy way to do this from the OAuth Mapping rule. Here I am not only adding things like the... Continue Reading →
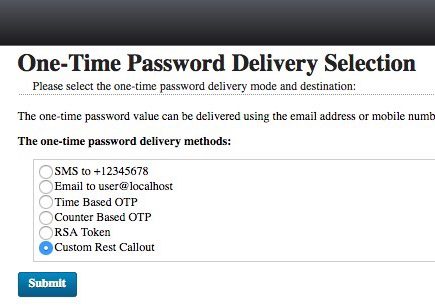
ISAM create a new OTP Mechanism
I wanted to make a new OTP Mechanism that was called by a JavaScript REST call - that wasn't the SMS mechanism in the box. In this example - I tested it with Boxcar - an iOS App that lets you send Push notifications with a simple REST call. To add a custom mechanism to... Continue Reading →
ISAM OAuth – Get credential attributes during an Authorization Code Flow
When performing an Authorization Code flow, or when performing an Implicit Grant flow, it may be necessary to get attributes out of the ISAM Session credential, and store them with your OAuth tokens. This is a quick guide to show how this can be done: Identify the request in the mapping rule Requests passing through... Continue Reading →
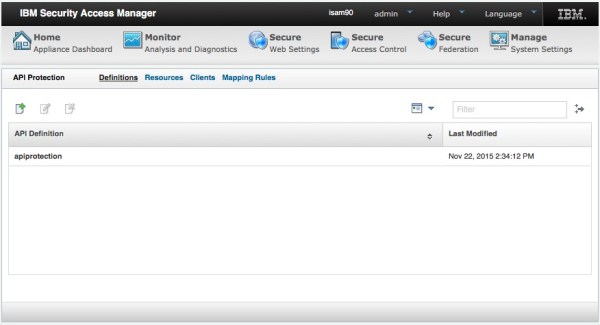
ISAM OAuth Token Mapping Rules – Beginners Guide
The ISAM OAuth implementation is exceedingly flexible. If you are just looking to do basic OAuth flows, then chances are you won't ever even look in these OAuth Mapping Rules. On the other hand, if you're looking to modify the behaviour of the OAuth flow to achieve OAuth nirvana, then these Mapping Rules are going... Continue Reading →
ISAM Advanced Access Control – HTML Email template
In ISAM 9.0.1 it's possible to use a rich text email template for Email One Time Passwords. There is a knack to setting it up though, you need to add the HTML to the XML template file using CDATA tags like the example below:
Commonly Overlooked ISAM Settings for production deployments
The ISAM Reverse Proxy has a wealth of settings that can be configured. This means that almost every deployment situation can be catered for, but also means that its easy to overlook some settings that may give you grief. In this post, I've decided to capture some of the more important ones to help you... Continue Reading →
Developing a client with OAuth and IBM Security Access Manager
IBM Security Access Manager provides a set of capabilities that can be used for authentication and authorization of a client accessing API's and can be scoped to a user or clients needs. When you moving away from browser use cases, REST based API's depend less on session cookies and instead make use of security tokens.... Continue Reading →
OAuth Auth ISAM authentication level mapping
ISAM provides the concept of Authentication Levels out of the box. This means a given authentication mechanism or flow can be assigned an integer value >0 that represents the authentication strength. OAuth Auth can make use of this for features such as incremental authentication - for example if the OAuth grant was issued via single... Continue Reading →
Setting an Authentication Level for Kerberos in ISAM
Tying an authentication mechanism to an authentication level can be very useful when writing security policy in ISAM. For example you might want a password based authentication (Such as Basic Auth or Forms Auth) to map to level 1, whilst you might hold a federated identity, or something achieved through another EAI to have a... Continue Reading →
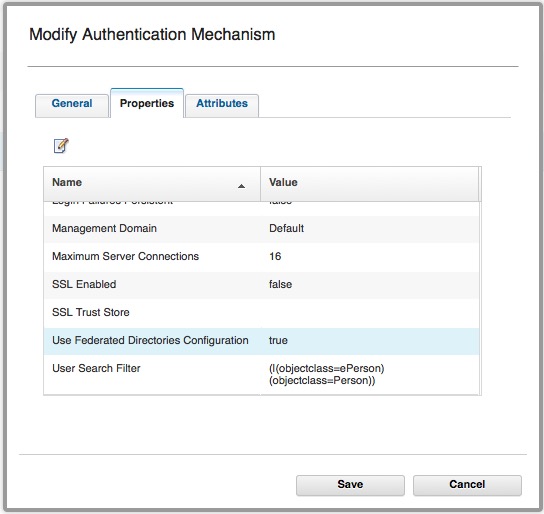
Using Basic Users with OAuth-Auth and ROPC
It is possible to use Basic Users with the ISAM OAuth-Auth capabilities. (ISAM Basic users are users that have NOT been imported into the ISAM registry.) Authentication used to be performed by: isAuthenticated = PluginUtils.isValidUsernamePassword(username, password); I've talked about how this is configured here. This authentication mechanism *can* be configured to use Federated Registries, however... Continue Reading →
IBM Security Access Manager (ISAM) Kerberos Configuration Guide
My colleague has posted an in depth set of articles on IBM DeveloperWorks for Kerberos configuration with ISAM. It covers both Kerberos integration's, being Desktop SSO with Kerberos into ISAM, and junctioning to servers using Kerberos for Junction SSO. The article is available here: https://www.ibm.com/developerworks/community/wikis/home?lang=en#!/wiki/W746177d414b9_4c5f_9095_5b8657ff8e9d/page/Information%20and%20Guides%20for%20Kerberos%20SSO
ISAM Forms SSO into BMC Remedy
Updated 09/2015: HTTP 505 error solved. See end of article. On a customer site, I encountered BMC Remedy, and had to perform SSO into the Application from ISAM. My initial attempt included trying to use the standard integration we have with Tomcat versions, as detailed here: http://www-01.ibm.com/support/docview.wss?uid=swg24021393 Unfortunately, this didn't work in the time I'd... Continue Reading →
ISAM EAI Server Error: 0x38cf042f
When trying to configure an EAI, I encountered the following error whenever it was supposed to be authenticating the user: Server Error Access Manager WebSEAL could not complete your request due to an unexpected error. Diagnostic Information Method: GET URL: <url> Error Code: 0x38cf042f Error Text: Server Error Solution Provide your System Administrator with the... Continue Reading →
ISAM Appliance Networking Changes
In ISAM v8.0.1.2, some fairly significant changes were introduced to the Management of the ISAM appliance networking interfaces. The update removed the concept of separate NICs for Application and Management interfaces and instead bound those concepts to an IP Address. It added support for VLAN tagging on packets, and provides a number of enhancements around... Continue Reading →