In ISAM 9.0.2, we released native appliance based capabilities to perform User Self Care Operations with ISAM.
The user self care operations are built using the authentication service which means operations are modular, can easily be reordered or customised to suite your flow.
Out of the box, there are three USC operations included:
- USC Account Create
New user enrollment policy, requiring reCAPTCHA and email validation. - USC Lost ID
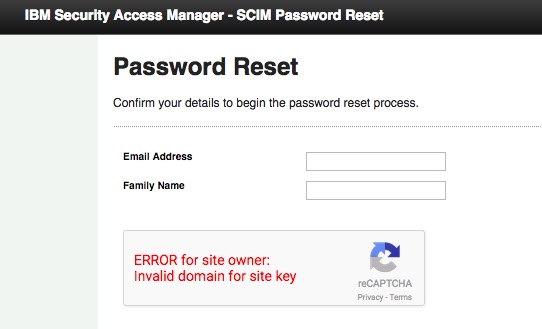
Lost ID policy, requiring reCAPTCHA, emailing your user id.. - USC Password Reset
Password reset policy, requiring reCAPTCHA and email one-time-password.
Here is an example of the steps used for an password reset flow:

If we wanted to make our own flow, we can make use of the existing mechanisms, to develop something to suit the needs of your organisation.
The main tools available for customising these flows are a number of new features with ISAM 9.0.2:
- ISAM SCIM Interface. (System for Cross Domain Identity Management)
ISAM now supports the standards based API for User object operations – SCIM.
This is capable of a full range of CRUD operations on users, with access configured either as an admin, or as operations performed on your ‘self’. - The JavaScript Authentication Service Module – InfoMap.
This is a general purpose module that can be infinitely customised in JavaScript to collect information from a user, present information to a user, validate information against external services, and call the new ISAM SCIM endpoint. - The Email Message Mechanism.
An easy way to send a notification to the user in authsvc flows.
This might be to ‘notify’ of a login, or notify of a specific operation such as registering a new browser device into ISAM. - The reCAPTCHA mechanism.
Finally an easy way to reduce the impact of bots on your ISAM deployment.
This can be validated as its own ‘mechanism’, or can be validated in any page presented by the Infomap module, using a JavaScript function. - Out of band mobile multi factor authentication – with IBM Verify and the ISAM Mobile SDK.
This is huge topic, and will need a separate post.
And of course all the existing mechanisms to verify a users identity:
- Username and Password mechanism
- Knowledge Questions
- The End User License Agreement module
- The OTP modules (SMS, Email, Time/Counter Based Soft token OTPs) etc.
- RSA Tokens
- Certificate Authentication
- Custom modules, including integrations with Yubikey etc.
For example, here I mocked up a scenario where a user could unlock their account when they presented a second factor authentication mechanism in the form of a Time based OTP (OATH), as generated by IBM Verify:

Here you can see I’ve used a selection of existing mechanisms from the standard password reset flow – such as the page that requests the email address and surname:
Each of the modules can be configured to return a specific template page (or multiple) from the available templates.
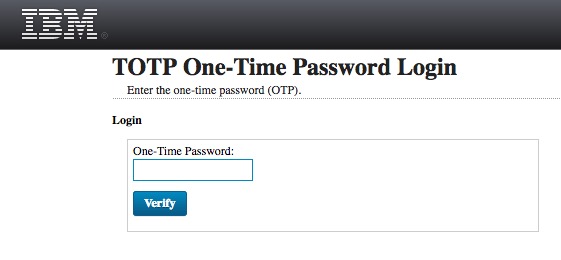
The next step, presents the user with the standard TOTP login page:

And then, once satisfied, will have their account unlocked.
In another example, I’ve developed a module that will authenticate the user against Facebook, and could use information received from Facebook to pre-fill an account page or just automatically create a local account in ISAM. A formal guide on this is pending, but let me know in the short term if you’d like to try it out.

