Over on the ISAM blog on ibm.com, I've just completed an indepth article on using ISAM with a Single Paged Application. These are typically applications that use JavaScript, AJAX, Angular and other frameworks to make a very dynamic user experience on a website. Think of any site you've used where the whole page doesn't reload... Continue Reading →
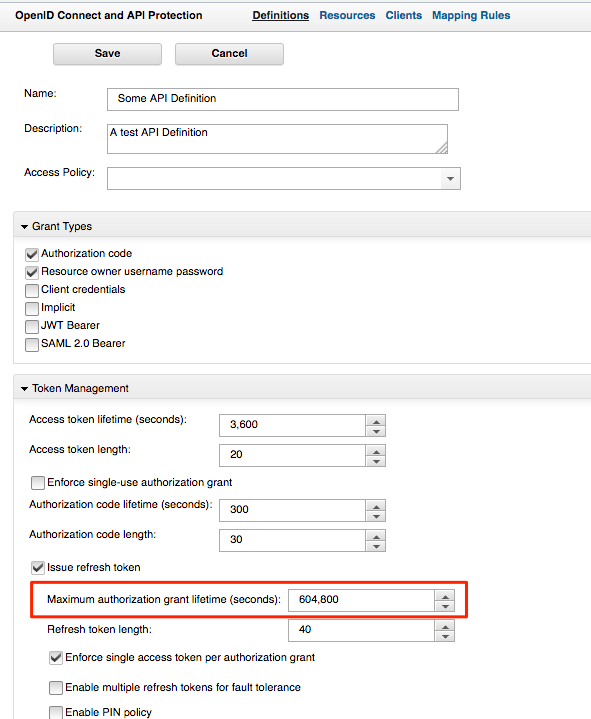
ISAM OAuth Inactivity
Its not immediately obvious, and commonly misconstrued as an problem of disappearing tokens, but the OAuth grants in ISAM have a "Maximum" Grant lifetime, as opposed to an inactivity in a default API Definition. This means that when you request a Token - say via ROPC and you are using the default settings of an... Continue Reading →
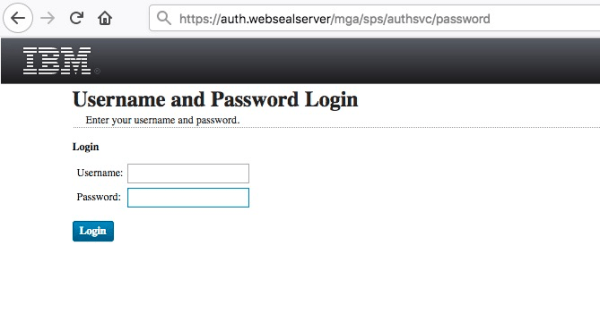
Simpler ISAM Authentication Service URLs
This article is no longer necessary, thanks to OOTB behavior available in ISAM 9.0.6 and later. See details here. In order to clean up the instantiation URLs generated by the authentication service, you can use a ISAM HTTP transformation rule. I've just completed two examples of this. Remove PolicyId static prefix: No static Prefix This... Continue Reading →
ISAM – Infomap – Any alias authentication
A number of customers like to use various alias's to authenticate into ISAM, up until recently, the primary way of achieving this, is via a Custom EAI, or some elaborate LDAP hackery. Infomap, and the UserHelper capabilities, makes this a much easier affair. Here is an example, where we use the infomap to authenticate based... Continue Reading →
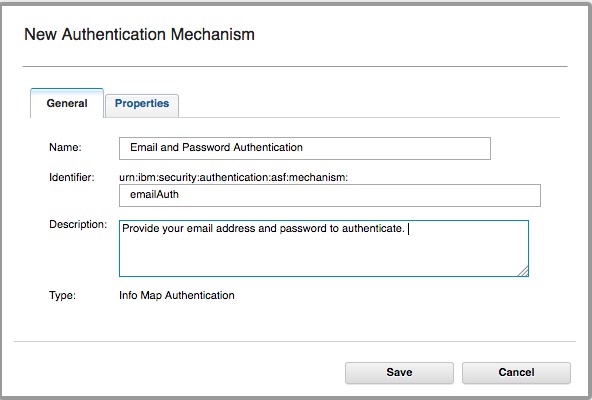
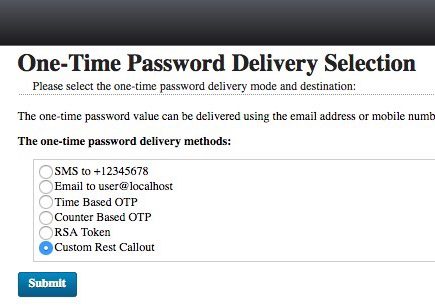
ISAM create a new OTP Mechanism
I wanted to make a new OTP Mechanism that was called by a JavaScript REST call - that wasn't the SMS mechanism in the box. In this example - I tested it with Boxcar - an iOS App that lets you send Push notifications with a simple REST call. To add a custom mechanism to... Continue Reading →
IBM Security Mobile Access SDK
Coinciding with the ISAM 9.0.2 release, we released version 1.2 of the IBM Mobile Security SDK for Android and iOS. ISAM SDK offers a platform library to: Authenticate users against ISAM with OAuth Works with OAuth for ISAM 8.0.1.3 onwards. Strong authentication Support Generate Soft Token One Time Passwords Time based OTP and Counter based... Continue Reading →
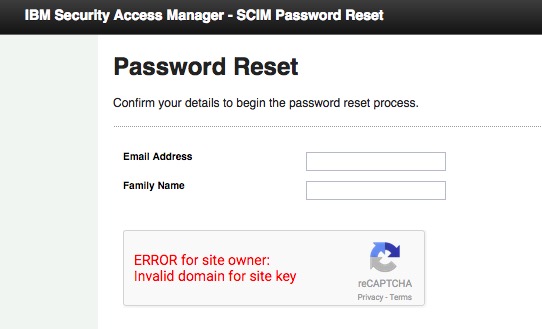
Password Reset with ISAM User Self Care
In ISAM 9.0.2, we released native appliance based capabilities to perform User Self Care Operations with ISAM. The user self care operations are built using the authentication service which means operations are modular, can easily be reordered or customised to suite your flow. Out of the box, there are three USC operations included: USC Account... Continue Reading →
ISAM Basic Users (aka Lite Users) vs Federated ISAM users
ISAM introduced the concept of non-imported users which we named Basic users, or lite users depending on who you ask, back in 2014 with version 8.0.0.4. I still regularly receive a bunch of questions as to what this means from an architectural perspective, and most importantly, what are the advantages and disadvantages to this new... Continue Reading →
ISAM OAuth Token Mapping Rules – Beginners Guide
The ISAM OAuth implementation is exceedingly flexible. If you are just looking to do basic OAuth flows, then chances are you won't ever even look in these OAuth Mapping Rules. On the other hand, if you're looking to modify the behaviour of the OAuth flow to achieve OAuth nirvana, then these Mapping Rules are going... Continue Reading →
Commonly Overlooked ISAM Settings for production deployments
The ISAM Reverse Proxy has a wealth of settings that can be configured. This means that almost every deployment situation can be catered for, but also means that its easy to overlook some settings that may give you grief. In this post, I've decided to capture some of the more important ones to help you... Continue Reading →
Set an authentication level for an Authentication Service Mechanism
Have been trying to setup an authentication service Mechanism to return a specific Authentication level into WebSEAL, and initially had some trouble, here is what you need to do: The important part are these lines: if (policyID.equals("urn:ibm:security:authentication:asf:hotp")) { stsuuAttrs.setAttribute(new Attribute("AUTHENTICATION_LEVEL", null, "5")); } Where you specify the policyID, and nominate the appropriate Authentication Level.... Continue Reading →
Developing a client with OAuth and IBM Security Access Manager
IBM Security Access Manager provides a set of capabilities that can be used for authentication and authorization of a client accessing API's and can be scoped to a user or clients needs. When you moving away from browser use cases, REST based API's depend less on session cookies and instead make use of security tokens.... Continue Reading →
ISAM Selective use of Local Response Redirect
In ISAM using the Local Response Redirect capability has traditionally been overkill when using it for an EAI for a login operation. The reason being, almost any error or management page that is traditionally handled by ISAM now gets redirected to your EAI. Including Login operations, Logout page, Stepup and other authentication related operations. It... Continue Reading →
Advanced ISAM Session Timeout capabilities
Sometimes it might be necessary to manage a session lifetime based on business or security factors, and these might need to be specific to an operation in progress. Here are some helpful techniques for managing the timeouts more dynamically: Understanding Session timeout accuracy Before we go into more detail of setting the session timeouts - it's... Continue Reading →
IBM Security Access Manager (ISAM) Kerberos Configuration Guide
My colleague has posted an in depth set of articles on IBM DeveloperWorks for Kerberos configuration with ISAM. It covers both Kerberos integration's, being Desktop SSO with Kerberos into ISAM, and junctioning to servers using Kerberos for Junction SSO. The article is available here: https://www.ibm.com/developerworks/community/wikis/home?lang=en#!/wiki/W746177d414b9_4c5f_9095_5b8657ff8e9d/page/Information%20and%20Guides%20for%20Kerberos%20SSO