Since the move to the ISAM for Web Appliance, certificate mapping for client authentication is performed by an XSL stylesheet mapping mechanism.
Since it was not immediately obvious to me, I’ve included two examples here where the CN of the certificate, is used as the username for the user in ISAM.
Provide Full LDAP DN:
In order to use this in your environment, just change the LDAP DN prefix/suffix in the sample below.
<?xml version="1.0" encoding='UTF-8'?>
<xsl:stylesheet xmlns:xsl="http://www.w3.org/1999/XSL/Transform"
xmlns:stsuuser="urn:ibm:names:ITFIM:1.0:stsuuser" version="1.0">
<xsl:output method="text" omit-xml-declaration="yes" encoding='UTF-8'
indent="no"/>
<xsl:template match="text()"></xsl:template>
<xsl:template match="/XMLUMI/stsuuser:STSUniversalUser/stsuuser:AttributeList">
!uid=<xsl:value-of select="stsuuser:Attribute[@name='SubjectCN']/stsuuser:Value"/>,cn=Users,o=ibm,c=AU!
</xsl:template>
</xsl:stylesheet>
Provide ISAM Shortname:
<?xml version="1.0" encoding='UTF-8'?>
<xsl:stylesheet xmlns:xsl="http://www.w3.org/1999/XSL/Transform"
xmlns:stsuuser="urn:ibm:names:ITFIM:1.0:stsuuser" version="1.0">
<xsl:output method="text" omit-xml-declaration="yes" encoding='UTF-8'
indent="no"/>
<xsl:template match="text()"></xsl:template>
<xsl:template match="/XMLUMI/stsuuser:STSUniversalUser/stsuuser:AttributeList">
!<xsl:value-of select="stsuuser:Attribute[@name='SubjectCN']/stsuuser:Value"/>!
</xsl:template>
</xsl:stylesheet>
Extract username from email/domain prefix:
If the CN in your certificate is philip@philipnye.com and you wanted the username ‘philip‘ you can use this mapping rule:
<?xml version="1.0" encoding='UTF-8'?>
<xsl:stylesheet xmlns:xsl="http://www.w3.org/1999/XSL/Transform"
xmlns:stsuuser="urn:ibm:names:ITFIM:1.0:stsuuser" version="1.0">
<xsl:output method="text" omit-xml-declaration="yes" encoding='UTF-8' indent="no"/>
<xsl:template match="text()"></xsl:template>
<xsl:template match="/XMLUMI/stsuuser:STSUniversalUser/stsuuser:AttributeList">
<xsl:variable name="cn" select="concat(stsuuser:Attribute[@name='SubjectCN']/stsuuser:Value, '@')"/>
!<xsl:value-of select="substring-before($cn, '@' )"/>!
</xsl:template>
</xsl:stylesheet>
To use them:
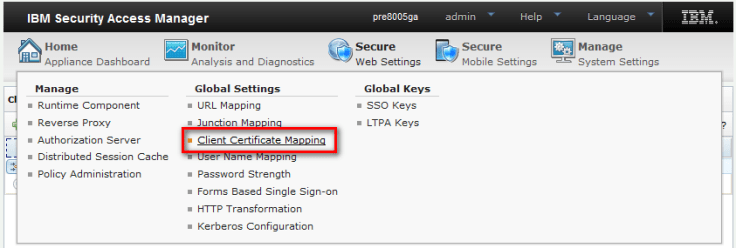
Secure Web Settings -> Client Certificate Mapping.
Deploy the changes.

After creating the mapping rule, simply configure the mapping in the following stanza:
[cert-map-authn] #The name of therules file which will be used by the certificate mapping # CDAS. # #The following files are currently available for this configuration entry: # mappingrule.xsl rules-file = mappingrule.xsl
WebSEAL trace
You can use the component pd.cas.certmap for trace, and it will help you troubleshoot your mapping.
Testing without using WebSEAL
Since this XSL is just converting an XML representation of the certificate into the username, it’s possible to mimic this behavior with an XSL test tool. I found this one worked. Using the trace tool above, you can get the XML representation for your certificate.
Sample certificate XML from my certificate here:
<?xml version="1.0" encoding='UTF-8' ?> <XMLUMI> <stsuuser:STSUniversalUser xmlns:stsuuser="urn:ibm:names:ITFIM:1.0:stsuuser"> <stsuuser:Principal> <stsuuser:Attribute name="name"> <stsuuser:Value>CN=pppuser1,O=IBM,C=AU</stsuuser:Value> </stsuuser:Attribute> </stsuuser:Principal> <stsuuser:AttributeList> <stsuuser:Attribute name="SubjectCN"> <stsuuser:Value>pppuser1@IBM</stsuuser:Value> </stsuuser:Attribute> </stsuuser:AttributeList> </stsuuser:STSUniversalUser> </XMLUMI>

The output between the exclamation marks is what is presented to ISAM. It should result in either the ISAM shortname or the fully qualified LDAP DN of the user.
