Tying an authentication mechanism to an authentication level can be very useful when writing security policy in ISAM. For example you might want a password based authentication (Such as Basic Auth or Forms Auth) to map to level 1, whilst you might hold a federated identity, or something achieved through another EAI to have a... Continue Reading →
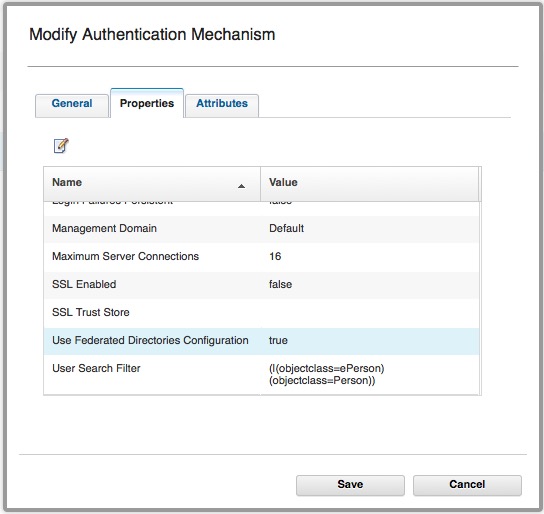
Using Basic Users with OAuth-Auth and ROPC
It is possible to use Basic Users with the ISAM OAuth-Auth capabilities. (ISAM Basic users are users that have NOT been imported into the ISAM registry.) Authentication used to be performed by: isAuthenticated = PluginUtils.isValidUsernamePassword(username, password); I've talked about how this is configured here. This authentication mechanism *can* be configured to use Federated Registries, however... Continue Reading →
Advanced ISAM Session Timeout capabilities
Sometimes it might be necessary to manage a session lifetime based on business or security factors, and these might need to be specific to an operation in progress. Here are some helpful techniques for managing the timeouts more dynamically: Understanding Session timeout accuracy Before we go into more detail of setting the session timeouts - it's... Continue Reading →
ISAM LMI REST API – HTTP 405 Method not Allowed Error
When using the REST API to run some commands against an ISAM for Web/Mobile Appliance, I ran into an HTTP error code that wasn't immediately obvious. Status Code: 405 Method Not Allowed There was no issue with the POST Method, but rather the headers that I sent. It's vitally important that you send the "Accept"... Continue Reading →
IBM Security Access Manager (ISAM) Kerberos Configuration Guide
My colleague has posted an in depth set of articles on IBM DeveloperWorks for Kerberos configuration with ISAM. It covers both Kerberos integration's, being Desktop SSO with Kerberos into ISAM, and junctioning to servers using Kerberos for Junction SSO. The article is available here: https://www.ibm.com/developerworks/community/wikis/home?lang=en#!/wiki/W746177d414b9_4c5f_9095_5b8657ff8e9d/page/Information%20and%20Guides%20for%20Kerberos%20SSO
ISAM Forms SSO into BMC Remedy
Updated 09/2015: HTTP 505 error solved. See end of article. On a customer site, I encountered BMC Remedy, and had to perform SSO into the Application from ISAM. My initial attempt included trying to use the standard integration we have with Tomcat versions, as detailed here: http://www-01.ibm.com/support/docview.wss?uid=swg24021393 Unfortunately, this didn't work in the time I'd... Continue Reading →
ISAM EAI Server Error: 0x38cf042f
When trying to configure an EAI, I encountered the following error whenever it was supposed to be authenticating the user: Server Error Access Manager WebSEAL could not complete your request due to an unexpected error. Diagnostic Information Method: GET URL: <url> Error Code: 0x38cf042f Error Text: Server Error Solution Provide your System Administrator with the... Continue Reading →
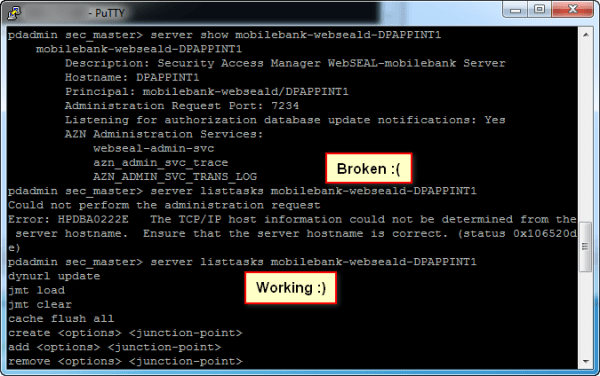
ISAM Error: HPDBA0222E
I started experimenting with ISAM for DataPower today, and in doing so, encountered a fun bug based on my environment. When creating a Junction, nothing appeared to happen. Eventually in attempting to debug using pdadmin on the DP Commandline interface, I ran the command: pdadmin sec_master> server listtasks mobilebank-webseald-DPAPPINT1 Could not perform the administration request... Continue Reading →
ISAM Appliance Networking Changes
In ISAM v8.0.1.2, some fairly significant changes were introduced to the Management of the ISAM appliance networking interfaces. The update removed the concept of separate NICs for Application and Management interfaces and instead bound those concepts to an IP Address. It added support for VLAN tagging on packets, and provides a number of enhancements around... Continue Reading →
Determine ISAM Appliance MAC Address
It can be a little confusing to get the MAC Address of the ISAM appliance network interfaces, which is particularly useful in virtualised environments. I've been in circumstances where you want to add/remove networking interfaces, but the order in which they are described in VMWare rarely corresponds to the order they are assigned when the... Continue Reading →
OAuth Authorization
When using ISAM in OAuth patterns, there are a number of ways you can do authorization based on OAuth scopes. In general, at last check, there are three main ways of Authorizing OAuth requests based on their scope. (or other attributes associated with the tokens). The mechanisms available are dependent on which OAuth validation mechanism... Continue Reading →
ISAM Authorization Rule for OAuth Scope
The vast majority of the work in developing this Authorization Rule was developed by my colleague Shane Weeden. Thanks for sharing Shane! Find more of his work here: https://www-304.ibm.com/connections/blogs/sweeden/?lang=en_us This authorization rule extracts the OAuth values of scope from the ISAM credential and applies a TRUE or FALSE authorization result subject to it containing the... Continue Reading →
ISAM Context Based Access PIP for OAuth
The vast majority of the work in developing this PIP was done by my colleague Scott Andrews. Thanks for sharing Scott! Find more of his work here: https://ibm.biz/securityintegration Building from the example PIP in my article here: ISAM JavaScript Policy Information Points here is a PIP that extracts the OAuth values of scope and supplies... Continue Reading →
SSO from Native Mobile application to Browser
I'm in the process of formalising an integration with ISAM for Web and ISAM for Mobile where we provide SSO from a Native mobile application into the mobile browser. If this is something you're interested in, please get in contact with me. I'm keen to hear your requirements. This pattern is particularly useful since... Continue Reading →
ISAM for Web – Different login pages per junction
Update 15/05/2015: It would seem that I may have over complicated this, we have a ISAM feature to do this already! 🙂 Apparently since TAM 6.1.1 we can use static management and error page templates per junction, as stated in the following technote: http://www-01.ibm.com/support/docview.wss?uid=swg21587936 So feel free to choose your own adventure! Different people access... Continue Reading →