ISAM Advanced Access Control has a mechanism that allows a developer to convert an authenticated/valid OAuth Access token, into an authenticated ISAM session, that is using a cookie. There are two useful scenarios that this endpoint comes in handy: Hybrid Apps Where an OAuth authenticated native application wants to open a WebView, that is authenticated... Continue Reading →
ISAM Advanced Access Control – HTML Email template
In ISAM 9.0.1 it's possible to use a rich text email template for Email One Time Passwords. There is a knack to setting it up though, you need to add the HTML to the XML template file using CDATA tags like the example below:
Set an authentication level for an Authentication Service Mechanism
Have been trying to setup an authentication service Mechanism to return a specific Authentication level into WebSEAL, and initially had some trouble, here is what you need to do: The important part are these lines: if (policyID.equals("urn:ibm:security:authentication:asf:hotp")) { stsuuAttrs.setAttribute(new Attribute("AUTHENTICATION_LEVEL", null, "5")); } Where you specify the policyID, and nominate the appropriate Authentication Level.... Continue Reading →
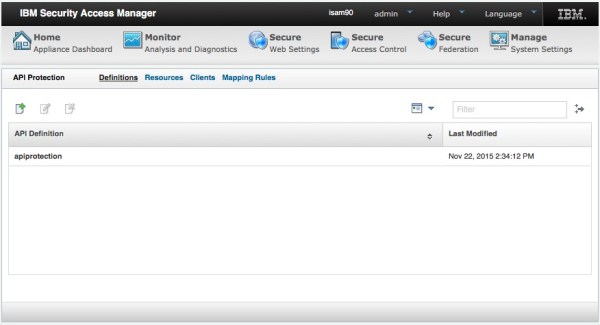
Developing a client with OAuth and IBM Security Access Manager
IBM Security Access Manager provides a set of capabilities that can be used for authentication and authorization of a client accessing API's and can be scoped to a user or clients needs. When you moving away from browser use cases, REST based API's depend less on session cookies and instead make use of security tokens.... Continue Reading →
ISAM Selective use of Local Response Redirect
In ISAM using the Local Response Redirect capability has traditionally been overkill when using it for an EAI for a login operation. The reason being, almost any error or management page that is traditionally handled by ISAM now gets redirected to your EAI. Including Login operations, Logout page, Stepup and other authentication related operations. It... Continue Reading →
OAuth Auth ISAM authentication level mapping
ISAM provides the concept of Authentication Levels out of the box. This means a given authentication mechanism or flow can be assigned an integer value >0 that represents the authentication strength. OAuth Auth can make use of this for features such as incremental authentication - for example if the OAuth grant was issued via single... Continue Reading →
Setting an Authentication Level for Kerberos in ISAM
Tying an authentication mechanism to an authentication level can be very useful when writing security policy in ISAM. For example you might want a password based authentication (Such as Basic Auth or Forms Auth) to map to level 1, whilst you might hold a federated identity, or something achieved through another EAI to have a... Continue Reading →
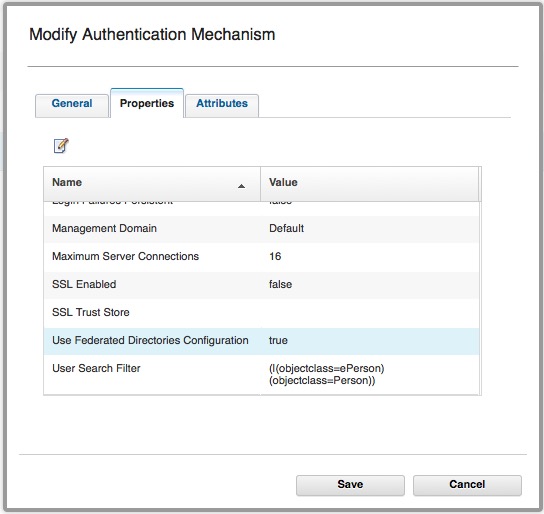
Using Basic Users with OAuth-Auth and ROPC
It is possible to use Basic Users with the ISAM OAuth-Auth capabilities. (ISAM Basic users are users that have NOT been imported into the ISAM registry.) Authentication used to be performed by: isAuthenticated = PluginUtils.isValidUsernamePassword(username, password); I've talked about how this is configured here. This authentication mechanism *can* be configured to use Federated Registries, however... Continue Reading →
Advanced ISAM Session Timeout capabilities
Sometimes it might be necessary to manage a session lifetime based on business or security factors, and these might need to be specific to an operation in progress. Here are some helpful techniques for managing the timeouts more dynamically: Understanding Session timeout accuracy Before we go into more detail of setting the session timeouts - it's... Continue Reading →
ISAM LMI REST API – HTTP 405 Method not Allowed Error
When using the REST API to run some commands against an ISAM for Web/Mobile Appliance, I ran into an HTTP error code that wasn't immediately obvious. Status Code: 405 Method Not Allowed There was no issue with the POST Method, but rather the headers that I sent. It's vitally important that you send the "Accept"... Continue Reading →
IBM Security Access Manager (ISAM) Kerberos Configuration Guide
My colleague has posted an in depth set of articles on IBM DeveloperWorks for Kerberos configuration with ISAM. It covers both Kerberos integration's, being Desktop SSO with Kerberos into ISAM, and junctioning to servers using Kerberos for Junction SSO. The article is available here: https://www.ibm.com/developerworks/community/wikis/home?lang=en#!/wiki/W746177d414b9_4c5f_9095_5b8657ff8e9d/page/Information%20and%20Guides%20for%20Kerberos%20SSO
ISAM EAI Server Error: 0x38cf042f
When trying to configure an EAI, I encountered the following error whenever it was supposed to be authenticating the user: Server Error Access Manager WebSEAL could not complete your request due to an unexpected error. Diagnostic Information Method: GET URL: <url> Error Code: 0x38cf042f Error Text: Server Error Solution Provide your System Administrator with the... Continue Reading →
ISAM Appliance Networking Changes
In ISAM v8.0.1.2, some fairly significant changes were introduced to the Management of the ISAM appliance networking interfaces. The update removed the concept of separate NICs for Application and Management interfaces and instead bound those concepts to an IP Address. It added support for VLAN tagging on packets, and provides a number of enhancements around... Continue Reading →
Determine ISAM Appliance MAC Address
It can be a little confusing to get the MAC Address of the ISAM appliance network interfaces, which is particularly useful in virtualised environments. I've been in circumstances where you want to add/remove networking interfaces, but the order in which they are described in VMWare rarely corresponds to the order they are assigned when the... Continue Reading →
OAuth Authorization
When using ISAM in OAuth patterns, there are a number of ways you can do authorization based on OAuth scopes. In general, at last check, there are three main ways of Authorizing OAuth requests based on their scope. (or other attributes associated with the tokens). The mechanisms available are dependent on which OAuth validation mechanism... Continue Reading →